SASE. What is it?
SASE: What is it?
We hear the term SASE a lot lately and are confident we are not the only ones. With the rapid advances in industry methodologies and approaches, we also know that some confuse SASE and SD-WAN. Are they the same? Are they complementary? What's the difference between them? Is SASE like SD-WAN v2.0? Let's find out.
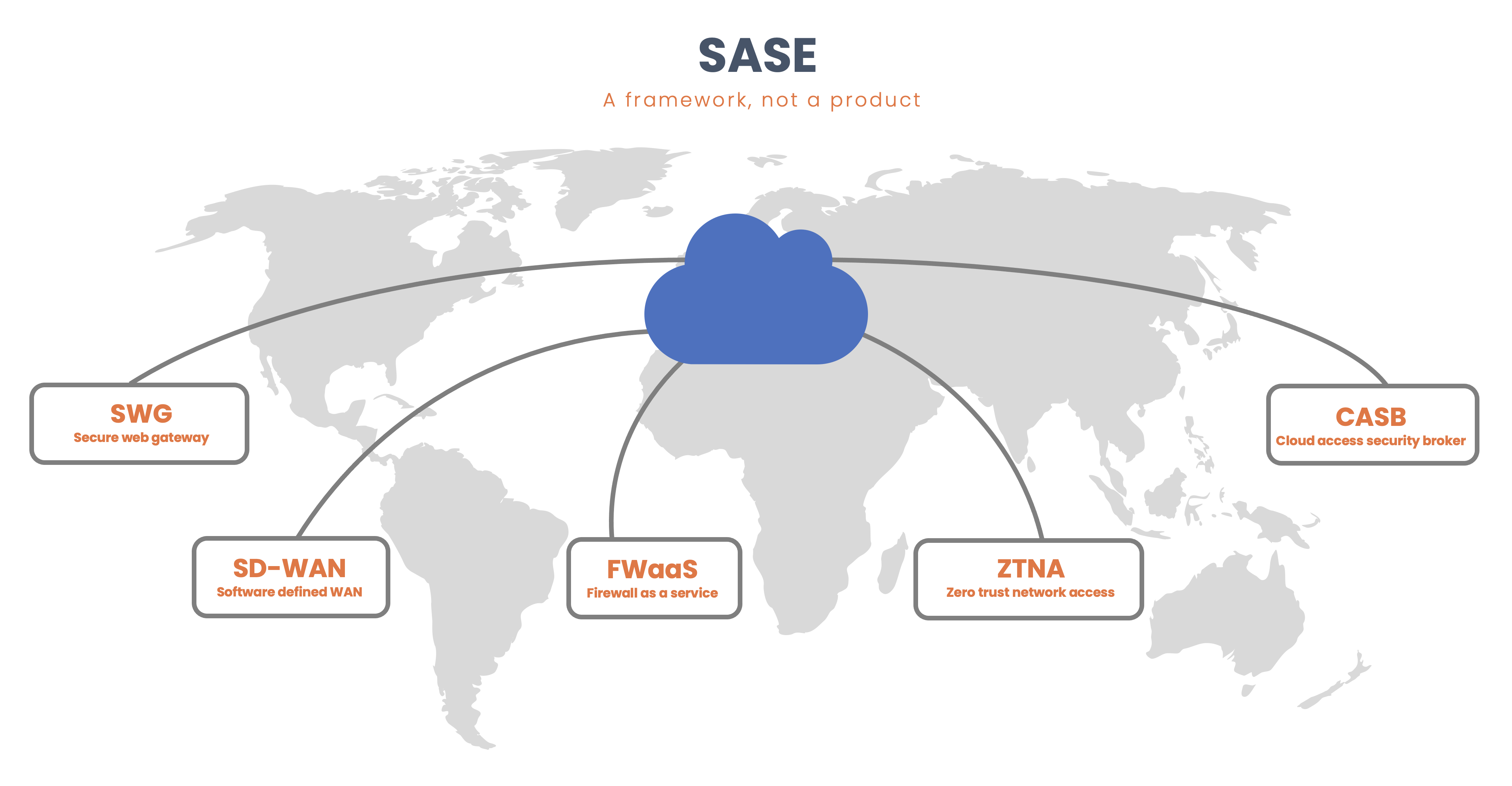
In 2019 the analyst firm Gartner defined the standards for a network architecture that combines VPN and SD-WAN capabilities with cloud-native security functions. For vendors, this has provided an opportunity to deliver their security functions as a cloud-hosted service. The architecture is made up of the following core components:
- Cloud Access Security Broker
- Secure Web Gateway
- Zero Trust Network Access
- FWaaS (Firewall as a Service, including features like AV/Malware protection, DLP, etc.).
- Software-defined WAN
When consumed as a package and integrated, the combination of the Network-aaS (as-a-Service), Applications-aaS, and Security-aaS capabilities and functionality is known as Secure Access Service Edge (SASE).
Gartner framework
Gartner defined the framework to address the historical need and challenges when providing security functions like web and email security; a company would deploy these functions in isolation from many different vendors and then experience trouble when trying to stitching them together. With the cloud providers offering competitive products and many companies using a cloud-first strategy, the security requirements have had to change to accommodate a widening edge that includes the following:
- Hybrid cloud/private cloud, with PaaS platforms like Azure, AWS, or GCP.
- SaaS platforms like Office365, ServiceNow, Salesforce, etc.
- Remote offices
- Roaming users
- The use of mobile devices
- Edge computing
- IoT devices.
Benefits
While most vendors approach SASE with the recommendation of using their entire portfolio to ease the adoption, the premise of the SASE framework is to transform end-to-end WAN and Security capabilities to cope with the growing desire to adopt cloud networking architectures. The benefits of this approach are many, for example:
- Reduced complexity: One vendor oversees all the security aspects against multiple devices from multiple vendors doing all these actions.
- A single-pass architecture: Traffic is inspected once by multiple policy engines instead of independently processing it on a chain of devices.
- Latency Optimization: Closer ingress and egress of traffic via geographically dispersed points of presence (PoP) are particularly beneficial for services like Video conferencing, IP Telephony, and generally speaking, collaboration applications as a whole.
- Trust Boundaries: A worker, anywhere in the world with Internet connectivity, can quickly and securely access any resource from any entity.
- Cost efficiency: By consolidating services and vendors, you can realize a reduced CAPEX and OPEX spend within your organization.
- Security consistency: A uniform set of policies, delivered once by the same provider defining the same security functions regardless of the source (application, user, or device) and destination (cloud or DC application).
Vendor implementations
Vendors like Fortinet and Cisco are leading their SASE frameworks from different viewpoints. Cisco has a large customer base that utilizes Duo Security, Cisco Umbrella, Cisco SD-WAN, and ThousandEyes. At the same time, Fortinet has a large customer base already using its appliances and services to provide a comprehensive security edge. Both are bringing tighter integrations between the components that define their SASE offerings. For example, Cisco introduced the Catalyst 8000 Edge Routers, and Fortinet introduced natively enabled ZTNA capabilities starting from FortiOS 7.0.
Some vendors may bundle additional services that are outside of the Gartner core components into their own SASE solution. For example, Cisco consider DNS Security to be a part of their SASE architecture. Although this isn’t a Gartner core component, it helps provide an additional layer of security for their specific offering. The solution of each vendor will vary considerably.
The main takeaway from working with our customers is that no two organizations are the same when adopting a SASE framework. Being flexible when approaching your SASE journey allows you to realize incremental wins along the way while building a solid foundation that is crucial to your future innovation. The main benefits of adopting a SASE framework is to simplify operations, reduce complexity, cut costs and consolidate vendors. Unfortunately there's not just a big SASE button that we can press to turn everything on. It's a journey which will take time and careful planning but if done correctly, the benefits and efficiencies will be well worth the investment.